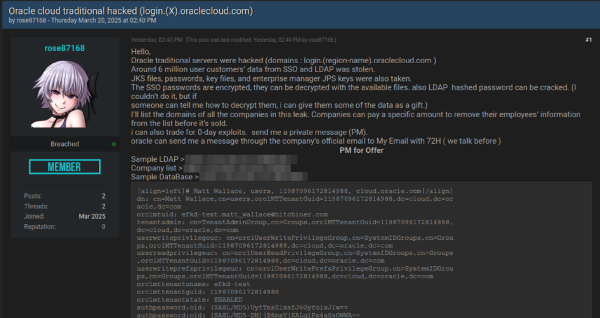
Somebody is claiming to have exfiltrated 6 million lines of data with Oracle Cloud’s SSO and LDAP that includes JKS files, encrypted SSO passwords, key files and enterprise manager JPS keys from servers on login.*.oraclecloud.com
The poster has no prior reputation, it is unclear if they're LARPing. Some of the sample data does align with prior infostealer logs, I'm told. https://breachforums.st/Thread-SELLING-Oracle-cloud-traditional-hacked-login-X-oraclecloud-com
#threatintel
The poster has no prior reputation, it is unclear if they're LARPing. Some of the sample data does align with prior infostealer logs, I'm told. https://breachforums.st/Thread-SELLING-Oracle-cloud-traditional-hacked-login-X-oraclecloud-com
#threatintel
Dieser Beitrag wurde bearbeitet. (2 Wochen her)

Kevin Beaumont •
Kevin Beaumont •
Kevin Beaumont •
https://web.archive.org/web/20250301161517/http:/login.us2.oraclecloud.com/oamfed/x.txt?x
Kevin Beaumont •
- YouTube
www.youtube.comKevin Beaumont •
Kevin Beaumont •
https://www.linkedin.com/posts/alon-gal-utb_big-i-just-received-10000-records-from-activity-7310017463516127232-XWbI
It’s unclear to me exactly what is happening with this one as the threat actor doesn’t appear to understand basic English grammar.. but there are signs something has happened at Oracle.
Big problem for Oracle as I’m not sure how plausible denials will be when threat actor, who sounds 12, is dumping data online.
Big - I just received 10,000 records from the Oracle breach, given to me… | Alon Gal | 45 comments
Alon Gal (www.linkedin.com)Kevin Beaumont •
I am still looking into this and will probably do a blog post this week. The threat actor is still dropping files everywhere and they do tend to point to a security incident at Oracle Cloud.
Kevin Beaumont •
https://www.bleepingcomputer.com/news/security/oracle-customers-confirm-data-stolen-in-alleged-cloud-breach-is-valid/
Kevin Beaumont •
Separately, the threat actor has shared what they claim to be current config files from Oracle Cloud servers with a different reporter.
I’m deliberately staying out of this one for now as I’m trying to finish Assassin’s Creed Shadows first.. but I think Oracle may have a pending PR disaster when the TikTok deal is due to complete.
Kevin Beaumont •
Oracle have not commented publicly on the breach, instead telling people to only talk to their CISO by phone, not in writing. They’ve sent out letters without Oracle letterheads, using external lawyers instead.
The behaviour going on at Oracle with cybersecurity is extremely alarming.
https://www.bleepingcomputer.com/news/security/oracle-health-breach-compromises-patient-data-at-us-hospitals/
Kevin Beaumont •
Now has an audio transcription https://github.com/j-klawson/oracle_breach_2025/blob/main/youtube_video_transcript.txt
(I’ve redacted the root passwords from screenshot)
oracle_breach_2025/youtube_video_transcript.txt at main · j-klawson/oracle_breach_2025
GitHubKevin Beaumont •
Kevin Beaumont •
Kevin Beaumont •
Oracle rebadged old Oracle Cloud services to be Oracle Classic. Oracle Classic has the security incident.
They’re denying it on “Oracle Cloud” by using this scope - but it’s their cloud service.
Kevin Beaumont •
Kevin Beaumont •
They are only doing so verbally, they will not write anything down, so they’re setting up meetings with large customers who query.
LukefromDC •
This is why when Oracle bought Sun Microsystems, OpenOffice (originated by Sun) was instantly forked as Libreoffice: to keep Oracle's mitts off of it.